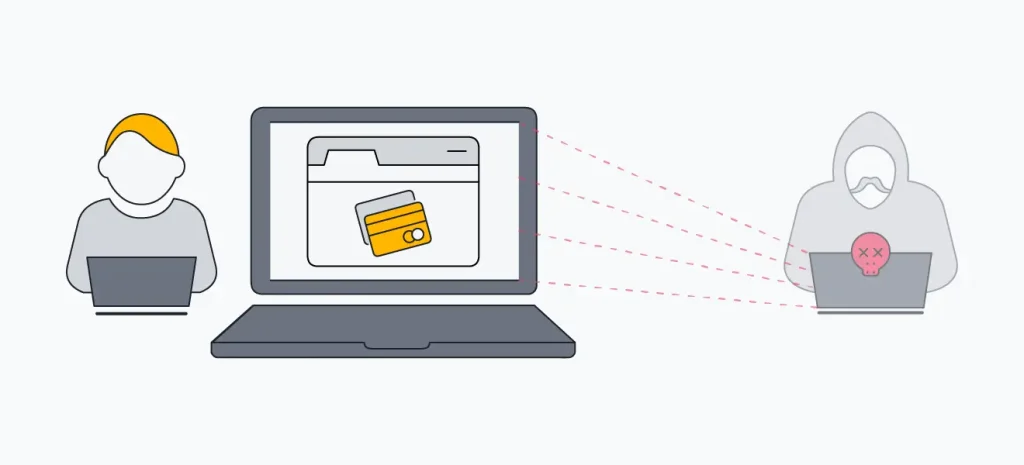
With cyber threats rampant in the digital age, you must secure your PC from hackers. The impact of cyberattacks may be devastating, including data breaches and loss of finance. However, there are practical and affordable ways of improving the overall security of a personal computer. This blog explores the ten most efficient practices to boost your PC’s cybersecurity.
10 Ways to Secure Your PC From Hackers:
- Install Antivirus Software:
Antivirus software itself forms an integral part of computer security. It finds and eliminates viruses & and malware to protect personal data or against identity theft, to provide all-around cyber safety. However, regular updates keep it effective; thus, it is an important factor in the creation of a safe online arena.
- Enable Firewall:
Firewalls are used to get protection against cyber attackers. It defends your computer or network from unnecessary traffic. It comes in two main types: Hardware as well as software that could be tailored to suit security-functionality compatibility needs. Real-time threat prevention can be achieved by incorporating regular monitoring in addition to built-in as well as third-party options. Updating the firewall is very critical in warding off any breaches and attacks.
- Connect Secure Sites:
It’s advisable to surf a website that has an SSL certificate. Secure Socket Layer (SSL) encrypts data ensuring information exchange between any browser and server. The padlock icon signifies that it is encrypted; trust is ensured by this cryptography. SSL helps to protect user data and avoids browser alerts. Be crucial while doing any online transactions, trust the sites that have installed SSL certificates. SSL encrypts your data and protects your sensitive information. Having an SSL certificate is also budget-friendly as there are cheap SSL certificate providers available in the market.
- Regular Software Updates:
Software updates are crucial to ensure the software’s proper functioning and overall effectiveness. Such updates incorporate crucial security patches that minimize hacks, decrease data breaches, improve the stability of the system, and confirm hardware compatibility. To be proactive is a step toward upholding cyber security, safeguarding personal information, and guaranteeing hiccup-free computing.
- Strong Passwords:
High-security passwords help prevent cyber-attacks or unwanted access to computers and data breaches. They ought to be complicated with capital and small letters, numbers, and particular symbols. It is important to avoid security threats, for instance by employing distinct passwords to access various accounts. Password managers will help in simplifying this as they generate passwords for you and store them securely. Security is also improved by using different passwords frequently and making sure that common mistakes are not committed. Further, two-factor authentication provides an additional layer of security by protecting personal and financial details.
- Two-Factor Authentication (2FA):
2FA is an important security layer for online accounts and it is a specific type of multi-factor authentication. This increases the level of security by requiring two types of verifications a password and an SMS sending it on your mobile device. Two-factor authentication (2FA) serves as an additional layer of protection in case passwords are stolen or compromised. It is easy to implement and is compatible with multiple services. In addition, it offers a strong digital safeguard that guarantees adherence to regulatory stipulations.
- Secure Your Wi-Fi Network:
It’s also important to secure Wi-Fi networks. Change the default router login parameters to deny a hacker entry. Enhance security with WPA3 encryption. Hiding your SSIS is additional protection, and updating router firmware closes down the holes. Keep unauthorized access out by using a stiff Wi-Fi password. Set up guest Wi-Fi network with additional control of the visitors.
- Beware of Phishing:
Beware of phishing when clicking on e-mail links or attachments. Always check the sender’s authentication, inspect email addresses, and avoid supplying personal data on questionable websites. Click on the links to check them out. Use antivirus/anti-phishing tools; tell of suspicious phishing messages & and teach others about tricks like these. Protecting Personal Information and Digital Security requires vigilance.
- Use a VPN:
With a Virtual Private Network (VPN), one can secure their internet and enjoy privacy. Using a VPN involves encoding an internet connection such that it cannot be accessed by any potential hacker or eavesdropper. These are especially useful when using public Wi-Fi for protection against data interception. Additionally, VPNs grant access to geo-restricted content and conceal one’s IP address from the public domain. Always opt for reputable VPN companies that have strict privacy policies on handshaking them through numerous devices and networks.
- Regular Backups:
Data Protection and recovery calls for regular data backup. These backups act as an insurance policy against data loss occurrences such as ransomware attacks, data corruption, or accidental deletion of sensitive data. This can provide an additional level of redundancy and facilitate rapid retrieval of lost data onto external drives or cloud storage. Automatic backups make this easier and a periodic test ensures its reliability. This practice is effective in protecting digital possessions that may compromise data loss.
Conclusion:
It’s a must to secure your PC against hackers in the digital scenario. Recognizing that cybersecurity is a never-ending journey requires continual surveillance and recognition of emerging dangers. In doing so, you’re employing important means of strengthening your digital environment for future safeguards.